
Open the VPN app and connect to a nearby server before launching the Tor Browser, and that’s it! With over 15 years of experience in content creation and digital publishing, he knows how to craft informative, useful content, with thorough research and fact-checking to back it up. He strives to make complex cybersecurity topics accessible and understandable to the broadest audiences. In his spare time, Michael likes writing fiction, reading murder mystery novels, and spending time with his family. Aside from government agencies, other entities, including corporations and hackers, could potentially monitor and track your movements across the dark web. Again, they can use various tools and technologies for this, like tracking tools or social engineering techniques.
It’s illegal to use the dark web for any form of criminal activity, like buying stolen goods, drugs, user accounts, and so on. The Tor Browser is an open-source web browser created for anonymous browsing and to evade censorship. It routes users’ traffic through thousands of volunteer-run servers called nodes/relays.
Quick Guide: Access The Dark Web Safely In 3 Steps
This means content of such sites isn’t accessible to web crawlers. That said, it’s worth noting that the Tor browser is not the same as a VPN. It connects you to a network of servers rather than a particular server. This makes it slower than a VPN and also very difficult to try and get a new IP address in a specific country, which is easy to do with a VPN.
Tor-over-VPN Vs VPN-over-Tor: The Right Order
If you live in the EU and want to know what data your provider has collected about you, the GDPR gives you the right to request a full report. However, it is often prohibited for ISPs to sell your data to third parties. With all this data, your ISP could create a very accurate profile of you and link it to your IP address.
Good Password Ideas And Tips For Secure Accounts
Even with Tor and a VPN, you’re not fully protected unless you also lock down your behavior. Most dark web leaks happen when users skip basic safety steps or reveal too much without realizing it. Use the tips below to patch common blind spots and avoid easy-to-make mistakes. Don’t log into any real accounts, reuse usernames, or enter any personal details. Treat every site as untrusted unless you’ve verified it from multiple sources. This hides your Tor usage from local networks, masks direct Tor connections, protects against network-level surveillance, and reduces the risk of being flagged for accessing privacy tools.
How To Get On The Dark Web In 2025: A Step-by-Step Guide
- SecureDrop is a site that protects the privacy of journalists and whistleblowers.
- You don’t want this suspicion because of the darknet’s reputation and notoriety.
- Files on the dark web can contain malware, ransomware, or other harmful software.
- As previously mentioned, the dark web is commonly used for illegal trade.
Law enforcement agencies worldwide monitor the dark web, and accessing these illicit markets, even out of curiosity, can draw unwanted attention and legal scrutiny. This process, though, can often involve accessing the dark web for research into the most current malware on the market. That being said, the anonymity offered by the dark web is the perfect breeding ground for criminals from all walks of life and users are advised to browse with extreme caution. Again, it’s DOT Security’s advice to stay off the dark web entirely. The dark web offers both benefits and risks for users going into it, but the intent of the user will also impact this.
The dark web refers to content on the internet that is intentionally hidden and requires special software like Tor Browser to access. The dark web is a subset of the deep web, which is all content on the internet that isn’t indexed by search engines. Norton 360 Deluxe provides a comprehensive suite of protection that can help block malware and dangerous links in real time, and even detect scams using cutting-edge AI detection. Plus, it features a built-in VPN to encrypt your connection, hiding your IP address and online activity, for more anonymous and private browsing. Once connected to Tor, you’re ready to begin exploring the dark web. However, keep in mind that the dark web is not organized like the regular internet.

Step 3: Securely Connecting To The Network
These computers are all owned by volunteers, passionate about privacy and happy to offer up their device to help others. Traffic is relayed through three nodes each time it passes through the Tor network. Everything else on the internet is located on either the deep web or the dark web – and they aren’t as easily accessible, or as safe. So if you’re planning on accessing the dark web, here’s all you need to know to access it safely.
Essential Safety Tips To Minimize Risks
It hosted over 7,000 .onion categorized links to make surfing the web easier. One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online. After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date. Since Tor has to pass your traffic through several nodes, it will slightly slow your speeds. You can use the Smart Location feature for the fastest connections. ExpressVPN is an excellent choice for Tor and accessing the Dark Web.
How Does Tor Browser Work?
Users need a special browser with added software to access the tor dark web in the first place. The open or surface web is what you access daily through search engines like Bing or Google. Before you even turn on the device, search engines have crawled through the web, looking for information, evaluating the sources, and listing your options.
- For instance, did you know you can unknowingly break the law while browsing the internet?
- And once they’re listed there, it’s nearly impossible to remove them.
- Look for features like real-time alerting, coverage of multiple dark web forums and marketplaces, credential and data leak detection, and integration with your existing security stack.
- Unfortunately, it requires you to have an invitation code to create an account.
- There are several whistleblower sites, including a dark web version of Wikileaks.
This is because the dark web is full of potentially dangerous content, and a VPN will help keep your identity and personal information safe. Without a VPN, you could be putting yourself at risk of being hacked or scammed. A VPN allows a user to encrypt all internet traffic traveling to and from his or her device and route it through a server in a location of that user’s choosing. A VPN, in combination with Tor, further enhances the user’s security and anonymity.
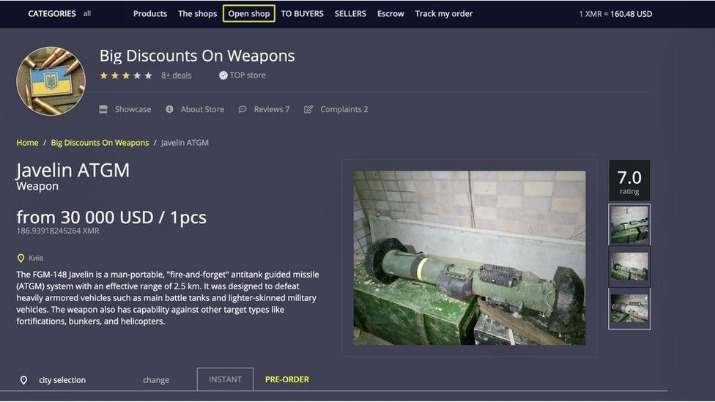
One study found that only 6.7% of Tor anonymity network daily users — a cohort that comprises mostly dark web users — connect to onion sites used for illicit activity. This essentially means that over 93% of Tor daily users use the dark web for legitimate reasons. Dark web encryption allows website owners and users to stay completely anonymous during their engagement. Cybercrime services, such as hacking tools and stolen databases, are available for hire, creating a marketplace for illicit online activities.
The worst part of the network is that you don’t have control over the nodes your traffic is routed through. There are no laws restricting access to websites on the dark web. However, using the dark web for illegal activity can be a criminal offense.
Instead, everything stays internal on the Tor network, which provides security and privacy to everyone equally. The deep web is crucial for maintaining privacy and security online, as it keeps sensitive information away from the prying eyes of the public and search engines. While the term “deep web” might evoke images of hidden, secretive content, most of it is just routine data stored on private networks. Now that your connection is active, it’s encrypted and untraceable by your internet provider.



