
Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe.
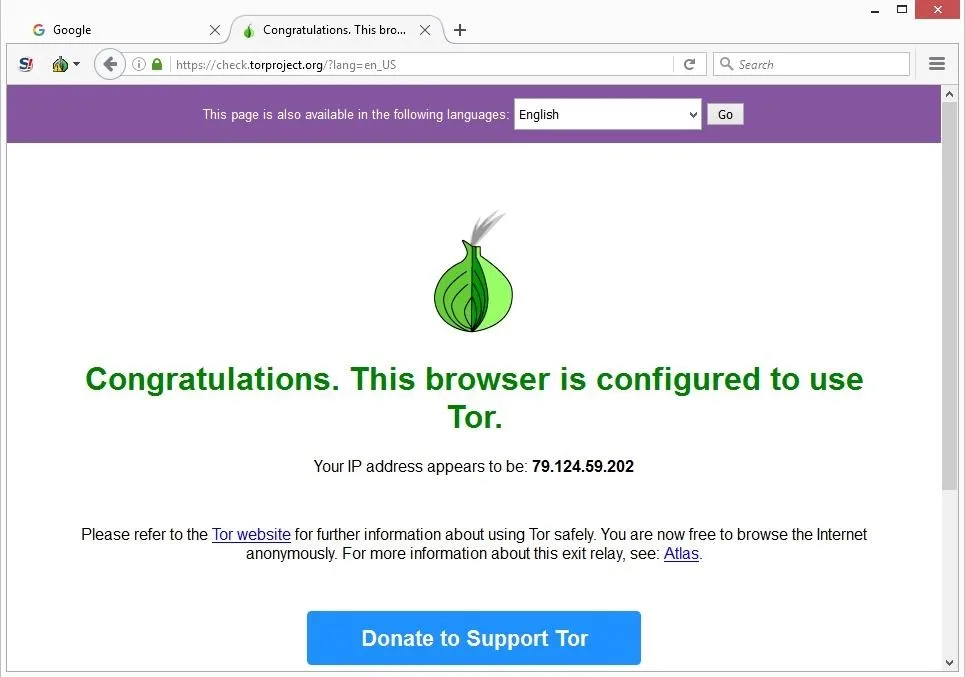
To say the least, DOT Security does not recommend going to the dark web unless absolutely necessary. However, if you’re going to venture into the dark web, you’ll need to be well–prepared, so keep reading to keep safe. Copy your desired onion URL and paste it into the address bar at the top of the screen to begin searching on the dark web. Alternatively, if the website has turned the onion URL into a link, you can click on that in the Tor browser, and it will automatically open the dark website. This guide will teach you how to install the Tor Browser in Windows easily so you can access the Dark Web or browse the web anonymously.

Hacking And Cybercrime Tools
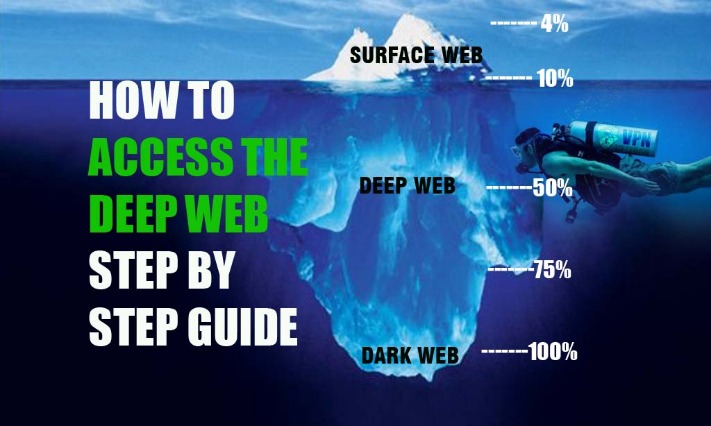
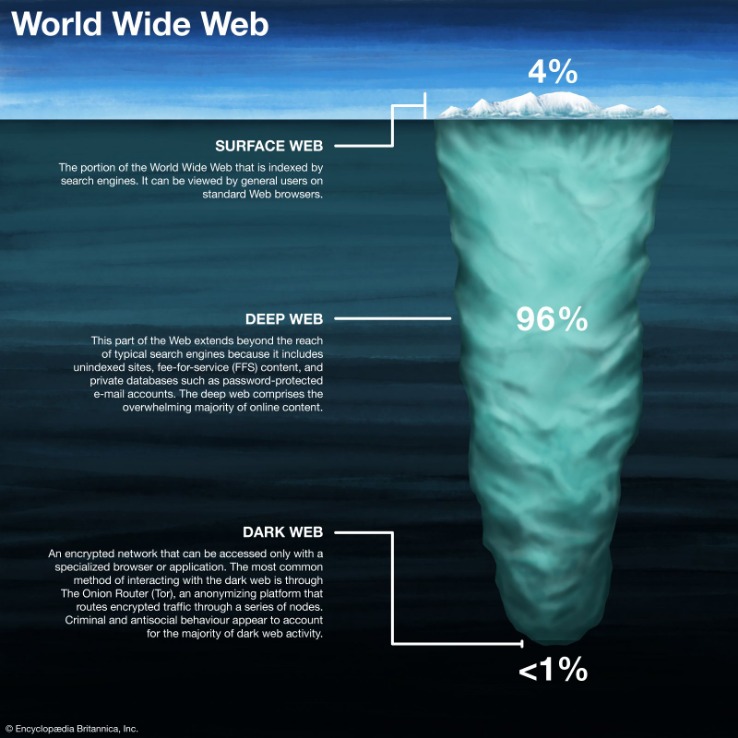
Many transactions on the dark web use cryptocurrencies like Bitcoin for anonymity. Ensure you understand how to use cryptocurrency wallets securely, and never keep large amounts in a single wallet. Use a separate wallet for dark web transactions to further protect your funds. While it may seem vast, the surface web actually makes up only a small fraction of the entire web. Think of it as the glossy shop windows of the internet — what you see is only what’s on display, neatly categorized and searchable. It is a relatively new provider but offers better features than most established VPNs.
Best Dark Web Sites 2025 – Detailed List
By keeping an eye on these alternative platforms and trends, you gain a deeper understanding of how privacy, anonymity, and underground markets adapt to new technologies and challenges. As digital ecosystems morph, staying informed and agile will help you make the most of evolving privacy tools—or avoid stepping into ever-more complex traps. VPN-over-Tor breaks dark web compatibility, reintroduces trust in the VPN provider, and creates unnecessary complexity.
Is It Legal To Access The Dark Web?
- On the surface web, you can contact your credit card company or law enforcement for help.
- You can choose the best darknet (.onion) website that suits you and start surfing.
- Second, shutting down or controlling access to the dark web would be a huge undertaking and could have unintended consequences.
- A VPN adds that extra layer of privacy you need when browsing the dark web on Tor.
On Tor, you can type in any URL you’d like to visit, including .onion links on the dark web. When accessing the dark web, the first step is to install a dark web-friendly browser on your computer. Unlike traditional browsers, this will route your internet traffic through an anonymizing network and mask your IP address. Unlike the publicly accessible surface web, the deep web includes sites requiring login credentials but is still accessible via traditional browsers. The dark web is a small, hidden subset of the deep web that requires special tools to access. By following these steps, you enter the Dark Web with more confidence and preparedness.
PRIVACY ALERT: Websites You Visit Can See These Details About You:
These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers. You won’t be able to access .onion addresses using a standard search engine as they aren’t indexed by crawlers. As search engine crawlers do not catalog these pages, you would need to know the exact link to access a website in this area of the internet. This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources. A VPN (Virtual Private Network) encrypts your internet traffic and hides your IP address before you access the Tor network.
Is Using The Dark Web Illegal?
For example, China blocks the Tor network IP addresses using the “Great Firewall”, and the Russian government has urged Internet Service Providers to block access to the Tor network. The deep web is significantly larger than the surface web, but it’s not inherently illicit or dangerous. In fact, most of the deep web consists of perfectly legal and functional services that are simply not meant for public access. The distinction between the deep web and the dark web is important to understand — while the dark web is part of the deep web, not everything in the deep web is hidden for nefarious reasons.
Cybersecurity Threats
Hyphanet (formerly Freenet) is another anonymous network that allows you to share and retrieve information without censorship. It’s designed for secure, decentralized storage and is often used for file sharing and accessing information anonymously. For advanced users, I2P offers configuration options for adjusting bandwidth limits, adding encryption layers, or even setting up your own eepsites. These settings can be found in the Router Console’s configuration panel. I2P (Invisible Internet Project) is an open-source network designed to allow anonymous and private communication. Although it’s not as widely used as Tor, I2P can provide robust anonymity and is well-suited for peer-to-peer file sharing.
From in-depth reviews to the latest news and how-to guides, PCMag is the go-to source for staying ahead in the digital world. Although the dark web represents a small fraction of the totality of the deep web, it has attracted perpetual media attention over the last few years. You need a special browser to access it, and when you do, your internet traffic is not wired through the network of interrelated public servers in the way it is when you access the surface web. Engaging with these sites, even inadvertently, can expose individuals to serious legal consequences, including criminal charges. Law enforcement agencies worldwide monitor the dark web, and accessing these illicit markets, even out of curiosity, can draw unwanted attention and legal scrutiny. With your VPN up and running and all of your other apps closed down, you’re finally on the brink of actually accessing the dark web.
Again, they can use various tools and technologies for this, like tracking tools or social engineering techniques. This is another reason it’s best to use a VPN and be careful on the dark web to preserve anonymity. A lot of the user data that gets stolen or leaked from big platforms ends up on the dark web, where users buy, sell, and exchange it among themselves. As explained earlier, you won’t be able to access the dark web the same way you would the surface web. You can’t type dark web addresses into your usual browser or search for them via Google.
Use directories like The Hidden Wiki or Dark.fail, which list verified and regularly updated onion links. Install Tor Browser from the official website, adjust security settings to “Safer” or “Safest,” and only use trusted onion links from verified directories. Cybersecurity Student → Conducts research on privacy tools → Accesses ethical hacking forums (legal) using Tor. Certain activities on the dark web are illegal in many countries. Ensure that you’re aware of what is permissible in your jurisdiction.
Tor Browser’s Great – But For More Complete Privacy Protection, You Need To Add This
Accessing the Dark Web, a part of the web that isn’t indexed by standard search engines, is not illegal in most countries. People use it for various legitimate reasons, such as bypassing censorship in restrictive countries. Law enforcement agencies in many countries monitor the dark web to combat illegal activities.
- The dark web is notorious for hosting marketplaces that deal in illegal goods and services, such as drugs, weapons, counterfeit money, stolen data, and even human trafficking.
- Browse responsibly to ensure your experience doesn’t lead to unwelcome surprises.
- You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe.
- It’s also used by journalists, advocacy group members, and political refugees in hiding.
We recommend that you use only the Tor browser to access the deep, dark web, if you must. If you fancy exploration, we’ve listed nine other options as well. It is made up of two virtual machines – a Gateway and a Workstation. All traffic must always go through the Tor network through the Gateway. This architecture protects your IP address even when the Workstation is before malware that may compromise it.
For this reason, users should be cautious when using their browsers. Therefore, you should understand the legal risks of accessing the dark web before you venture into this murky world. On the surface web, you can contact your credit card company or law enforcement for help. But the dark web operates like the Wild West—no rules, no protection. Cybercriminals often disguise malware within legitimate-looking files to trick users into compromising their own security.
However, not all countries are signatories, limiting their effectiveness. International bodies like the United Nations have advocated for a unified approach to cybercrime legislation. The UN Office on Drugs and Crime (UNODC) is working to develop an international legal framework to address cybercrime, including activities on the dark web. This initiative aims to harmonize laws across countries, facilitating prosecutions and international cooperation. In the European Union, the General Data Protection Regulation (GDPR) has influenced how personal data is handled, including on the dark web.
Without a VPN, you could be putting yourself at risk of being hacked or scammed. The dark web contains much of the internet’s illicit content, ranging from drug trafficking to child pornography sites. Like I2P, Freenet is a self-contained network within the network that can’t be used to access sites on the public web.



