
Strong vendor support, customizable alerts, and compliance alignment are also key to ensuring the tool delivers actionable insights, rather than just noise. The dark web is notorious for hosting a wide range of cyber threats that pose significant risks to individuals and organizations. One common threat is the sale of stolen credentials, including usernames, passwords, and financial information, which cybercriminals use for identity theft and fraud. Drugs are typically sold using cryptocurrency to maintain anonymity, and the buyers and sellers are often difficult to trace. These markets operate similarly to physical drug markets but are hidden from law enforcement through the use of the Tor network.
This article will explore the legality of the dark web, how it works, and what you need to know before accessing it. A VPN (Virtual Private Network) encrypts your internet traffic and hides your IP address before you access the Tor network. This extra layer of security ensures that your ISP and potential attackers cannot see that you’re using Tor. Although browsing the dark web is not illegal, it contains unsavory activities that can expose you to danger.
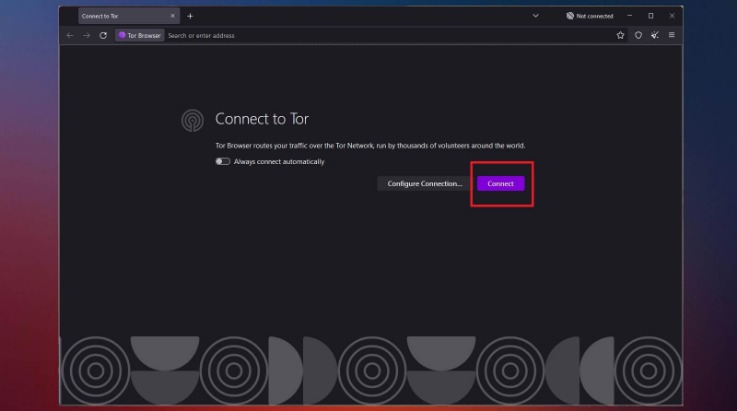
Tor Over VPN (Recommended)
A VPN will mask your location and stop the online breadcrumbs that can lead back to you. Connections made while a VPN is active will also be encrypted, helping you stay protected from eavesdropping and man-in-the-middle attacks. You can usually select the location you want to appear to originate from and VPNs will use a collection of servers and relays to make tracing your IP difficult. When the dark web is mentioned online, it is usually in tandem with criminal marketplaces and arrests made by law enforcement agencies. However, we strongly advise against using dark web marketplaces due to legal risks and the high likelihood of being scammed. Identifying specific individuals who use the dark web can be quite tricky.
But you can do this through using open-source encryption software such as Veracrypt. Using open-source means there’s far less chance of any security flaws or deliberate backdoors as the code is constantly reviewed by the community. Not only is browsing via tor more secure, it also is more private as it effectively shuts out online trackers. The Tor browser is based on Firefox and makes use of extensions like ‘NoScript’ to prevent harmful code from loading and there’s a built-in ad blocker (see below).
Finding Onion Sites

It is an excellent option if you want to surf the web anonymously. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. This article lists some of the best dark web websites you can visit securely. Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. Beyond DuckDuckGo, other options have failed to keep up with the evolving landscape. Though these browsers are effective at serving up dark web search results, the experience is reminiscent of browsing the web in the late 1990s.
WANT TO TRY THE TOP TOR VPN RISK FREE?

These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down. When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI. The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers.
The Best Dark Web Search Engines In 2024
These search engines work best if you already know what site you’re looking for, not for general browsing. Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. Facebook’s dark web version allows users to access the site where it is banned or restricted. Although the social application is known for collecting data on its platform, it does not like sharing the information with others.
Your Data Can End Up Landing Anywhere
By encrypting communication before it gets to the Tor network, pairing Tor with a VPN gives a second degree of protection. Research of the dark web is legal as long as national or international laws are not broken. People often have bad feelings about the dark web, but not everything on it is illegal or dangerous. In fact, journalists, privacy advocates and academics use it every day to protect their identities and get to material that has not been blocked. The beginning of the dark web is generally seen as coinciding with the release of Freenet in 2000.
Virtually anything you can buy on the surface or clear web you can also find on the dark web. Books, video games, apparel and rare collectibles are some of the legal items you can buy on dark web commerce sites. Samson has over 3 years of experience writing about VPNs for Cloudwards. Apart from his professional endeavors, Samson is passionate about soccer and enjoys reading, table tennis and watching sports in his spare time. He has also contributed to platforms like Financesonline.com and Timeero.com.
FAQs About Accessing The Dark Web Safely On Your Phone
The same applies to downloading files, which often contain tracker elements. You should avoid downloading files via Tor to maximize your anonymity. For example, in Safer mode, JavaScript is turned off on non-HTTPS (insecure) sites, but in Safest mode, JavaScript is turned off entirely for all sites.
Is Tor Completely Anonymous?
Because of these privacy features, the dark web remains a hidden but active part of the internet ecosystem. Whether your search engine of choice is Google, Bing, Baidu, Yahoo! The true internet – that which includes content not indexed by these search engines – is hundreds of times bigger. Content in the dark web is designed to be hidden and you’ll need special software to access it. The Tor browser is the most popular tool, though you can also use Freenet, ZeroNet, I2P, and Riffle. Once you’ve securely connected to the Dark Web via Tor, the next step is locating legitimate .onion sites.

How To Install Windows 11 With An Offline Account
If you plan to purchase on a dark net marketplace or dark web commerce sites, you’ll need to create a fake identity. Remember only to make purchases using digital currencies and never provide any online banking login details. As I mentioned above, the dark web is a decentralized, non-indexed network of web pages, and the sites don’t use standard URLs. There are marketplaces where people can sell stolen credit card numbers, conduct illegal drug transactions, and scam people out of their cash and crypto. Even in an era of increased online surveillance, the average person on the internet likely has too much to lose to bet on their safety for curiosity’s sake. Heck, I’m one of PCMag’s resident security experts, and I’m not playing around on the dark web just because I know how to.
- Certain activities on the dark web are illegal in many countries.
- I review privacy tools like hardware security keys, password managers, private messaging apps and ad-blocking software.
- In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere.
- If your information has been compromised, then it’s likely that your phone number is also on the dark web.
- However, with the right security measures and cautious browsing, you can minimize these dangers.
By distributing communication over several nodes, it obscures the user’s IP address. Indeed, most nations; including the United States, the United Kingdom, and India, allow access to the dark web as a lawful activity. Get Avast BreachGuard for Mac to protect your privacy and keep your personal data from falling into the wrong hands. Get Avast BreachGuard for PC to protect your privacy and keep your personal data from falling into the wrong hands.
The Tor browser is your gateway to the dark web, allowing you to access .onion sites anonymously. Arguably, the best-known tool used to access the dark web is the Tor Browser. The dark web (often referred to as the “darknet,” “black web” or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose.



