These options include Torch, NotEvil, Haystak, Candle and AHMIA. Though these browsers are effective at serving up dark web search results, the experience is reminiscent of browsing the web in the late 1990s. To better understand how the dark and the deep web work, you must first understand how the open web operates. Web crawlers run the regular internet, scouring the web to discover newly published websites or pages in a process called crawling. Anonymizing browsers are banned in some countries like China and Russia.
For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users. Do not use any personally identifiable information on the dark web. Use aliases and avoid any activity that might reveal your identity. I2P (Invisible Internet Project) is an open-source network designed to allow anonymous and private communication. Although it’s not as widely used as Tor, I2P can provide robust anonymity and is well-suited for peer-to-peer file sharing. This requires your connection to go through multiple nodes and relays, which will slow down browsing on Tor.
You don’t even need to use Tor Browser, but keep in mind other browsers can still pass identifying information through the network. Alternatively, there’s IPVanish who claim to be the world’s number one VPN for Tor and comes highly recommended, you can save 60% on the annual plan here. Obviously, finding these .onion websites is the first challenge, as they won’t show up in Google search results. You can’t just Google “Silk Road” and hope to land on the dark website.
Myth 4: The Dark Web Is Inherently Dangerous To Visit
As illustrated in the screenshot below, our request was routed through servers in Luxembourg, Germany, and Austria when visiting TechRadar.com. We’ve talked about the Tor protocol bouncing your traffic through multiple remote servers. However, seeing is believing, and the Tor browser allows you to see which servers your traffic passes through. The tradeoff is that you don’t get personalized search results, as DuckDuckGo doesn’t collect user data.
Is It Illegal To Use The Tor Browser?
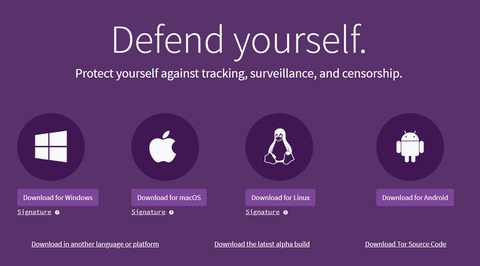
It’s important to note that not everything in this space is illicit; it serves as a refuge for privacy-conscious individuals and whistleblowers. Proton VPN also offers a one-click Tor connection option that lets you route all your PC’s internet traffic via the Tor Network. This is more or less the same process the Tor Browser uses to connect to its network, which is one of the safest alternatives to the Tor Browser when it comes to accessing onion sites. The Tor browser uses the Tor network, which was developed in the mid-1990s by US Naval Research Laboratory employees.
Malicious Software
By using Tor over VPN, the VPN encrypts your data and hides your IP address. This means that all of your traffic, including your Tor Browser activity, is protected. This does not protect you from malicious exit nodes, as your internet traffic is unencrypted by the time it reaches its destination.
Your Guide To Accessing The Dark Web On Your Phone
Choose your language and click “OK.” Follow the installation prompts. There are four nodes between your computer and the website you want to connect to. The browser uses a unique security system, which the United States Navy originally developed to protect the government’s intelligence communications. Dark web websites don’t bear Internet Corporation for Assigned Names and Numbers (ICANN) domains, such as .com. They use a scramble naming structure that combines a string of letters and numbers to create URLs that are impossible to remember. If you’re intrigued and want a firsthand experience, follow this guide to learn how to access the deep web with an anonymizing browser.
- We already went through VPNs, anonymizing web browsers, and disposable operating systems, so I won’t bother reminding you about those.
- From choosing the right networks and privacy tools to avoiding scams and malicious software, every step you take should be guided by caution and informed judgment.
- We love it because of its simplicity, which, as you saw, lets you visit the dark web in seconds.
- NinthDecimal is the leading media and technology service provider for the WiFi industry.
- Tor was developed in the mid-1990s by United States Naval Research Laboratory employees, mathematician Paul Syverson, and computer scientists Michael G. Reed and David Goldschlag.
- Its VPN Accelerator distributes the CPU load between multiple processes in OpenVPN, and modifies the servers’ Linux stacks to shorten the normal packet processing path.
How Do I Keep Myself Safe When On The Dark Web?

You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. However, there are plenty of legal and legitimate online activities that require privacy and anonymity. The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy.
How To Access The Dark Web Using The Tor Browser
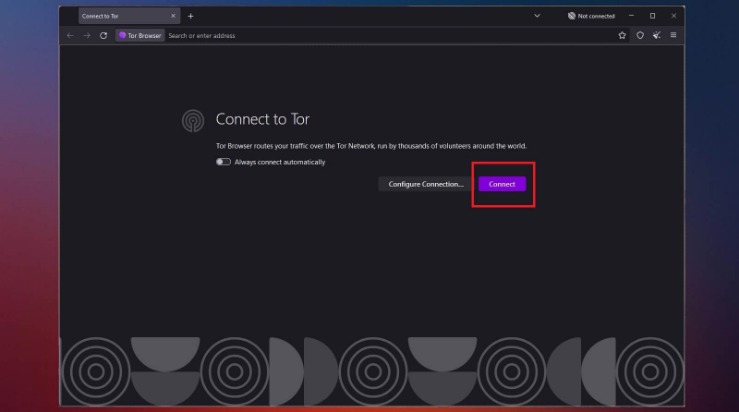
But this tradeoff is worthwhile when seeking to browse with the utmost privacy. Likewise, you’ll experience slower browsing speeds when browsing via Tor, as your requests get bounced through several servers before being processed. To surf the web privately, you need to connect to the Tor network from your browser. Manually implies clicking the Connect button each time you open Tor, while automatically means an automatic connection whenever you open the Tor browser. Open the downloaded file on your device to begin the installation process. The process is similar to installing any other software – follow the on-screen instructions and wait for the installation to complete.
The Tor protocol isn’t 100% failsafe, but it goes a long way in preserving privacy when surfing the web. The silver lining is that VPNs work on iPhones so you can mitigate the risk by connecting to one beforehand. We’ve clarified how to go on the dark web anonymously with the help of a VPN. A VPN is a confusing factor for many because there are two ways to use it with Tor. It might be because of the poorly maintained site or Tor’s slow speed because of the way it works.

The victim types in their information, thinking they’re accessing a site that they know and trust, but they’re actually giving away their data. There are a lot of these sites across the dark web, which is why you have to be extra careful. The easiest way to avoid falling victim to them is to simply not provide any personal data when browsing the dark web. Many cybersecurity and tech experts recommend using a VPN whenever you want to access the dark web via the Tor Browser or any other specialist browser. A quality VPN like ExpressVPN will encrypt your internet traffic and mask your IP address, providing an extra layer of anonymity when establishing the initial Tor connection.
- Many experts advise against using third-party mobile browsers that utilize the Tor Network.
- Law enforcers can use custom software to infiltrate the dark web and analyze activities.
- Manually implies clicking the Connect button each time you open Tor, while automatically means an automatic connection whenever you open the Tor browser.
- So, how do you venture into this enigmatic part of the internet safely?
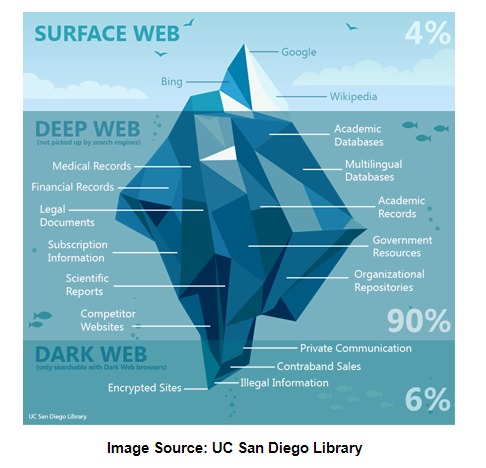
The dashboard should open properly, indicating you’re ready to connect to any VPN server. This is just the first but also very important step to go to the dark web anonymously. Funnily enough, the deep web is the largest part of the internet! It’s online and you can access it but your friend or family can’t.
In other words, these are pages that aren’t indexed and therefore can’t be found by a typical search engine. The dark web wasn’t the invention of a single individual but from efforts to build secure, anonymous communication. Its foundation is the Onion Router (Tor) project, developed in the 1990s with funding from the U.S. Naval Research Laboratory to protect sensitive government communications.
Components Of DOT Security’s Services
Well, as long as you don’t visit sites with underaged models or that engage in human tracking or that sell drugs and other illegal items. That’s a trick question, because there isn’t even a good free VPN, much less a best VPN. Freebie VPNs will track their users’ online usage, as they make money by selling this tracking info to advertisers and other nosy parties. One of the major advantages of using Tor in overly-restrictive countries is that it keeps your online travels private.



