
This involves passing internet traffic through the Tor network first, and then through the VPN. It’s a less recommended configuration, though it does offer protection against exit nodes run by those with malicious intent. Unlike the surface web, which can be indexed by standard search engines, the dark web exists on encrypted networks and hosts websites with random, complex URLs. This layered encryption and anonymization make it difficult for authorities or outsiders to trace activities or identify participants. Because of these privacy features, the dark web remains a hidden but active part of the internet ecosystem.
How To Make Google Calendar Dark Mode
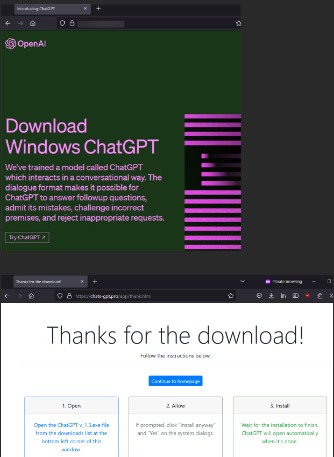
With over 15 years of experience in content creation and digital publishing, he knows how to craft informative, useful content, with thorough research and fact-checking to back it up. He strives to make complex cybersecurity topics accessible and understandable to the broadest audiences. In his spare time, Michael likes writing fiction, reading murder mystery novels, and spending time with his family. A phishing website or link is one that appears legitimate but is actually a trick designed to make you hand over your personal information to hackers and other bad actors. Often, these sites are made to look just like real, trusted platforms, such as banks, social media sites, or email providers. However, there are also perfectly legal, safe sites within the dark web, like privacy-focused forums, marketplaces, and more.
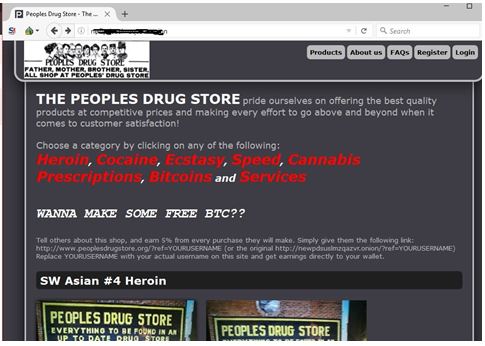
Marketplaces
- Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
- If you are curious about accessing the deep web, you are likely already using it daily through pending website redesigns, blog posts under review, and pages accessed during online banking.
- Internet providers and websites can detect when Tor is being used because Tor node IPs are public.
- This will help to protect you from malicious sites designed to steal your data or money.
- By understanding the nature of onion websites and using the Tor Browser for access, you can explore the Dark Web in a more informed and responsible manner.
Dark web marketplaces offer a range of both legal and illicit goods. Here’s a look at several of the illegal items you can buy — with prices — courtesy of Privacy Affairs’s Dark Web Price Index 2023. While some reports of dark web murder-to-order are overblown, it is possible to commission acts of cybercrime on the dark web.

Step 3: Adopt “operational Security”
These include buying or selling drugs, weapons, stolen data, malware, or hacking services, which are crimes. Sharing or even possessing abusive or exploitative content is also a very serious offense. Police do investigate and prosecute crimes that happen on the dark web.
Some sites might offer tutorials or guides for aspiring cybercriminals. In the deep net, web crawlers are blocked from accessing web pages to gather information for indexing, so the content remains hidden. Some content and services on the deep web are indexed by search engines, but paywalls or password protection prevent access.
Unverified Content And Hoaxes
To better understand how the dark and the deep web work, you must first understand how the open web operates. Web crawlers run the regular internet, scouring the web to discover newly published websites or pages in a process called crawling. Anonymizing browsers are banned in some countries like China and Russia. Moreover, given the nefarious nature of the dark web, some government agencies may set up Tor gateways to monitor what’s happening on the dark web. If you’re intrigued and want a firsthand experience, follow this guide to learn how to access the deep web with an anonymizing browser.
Is The Dark Web Only For Criminals?
Tor was originally developed by the United States Naval Research Laboratory to protect communication privacy. It accomplishes this by encrypting and routing internet traffic through a network of volunteer-operated servers, called nodes, resulting in a decentralized and obfuscated system. Public websites indexed by search engines (e.g., news sites, social media, blogs). Additionally, configure your security settings to provide maximum protection, such as firewall activation and using a VPN, while browsing the dark web. This helps safeguard your device from viruses, spyware and other malicious software.
Everything you can find with a Google search is part of the surface web. In other words, every part of the web you can see and access by browsing normally. When viewed through this lens, the dark web’s legality is based on how you as a user engage with it. You might fall to the wayside of legal lines for many reasons that are important for the protection of freedom. Others may act in ways that are illegal for the protection and safety of others.
Can Cybersecurity Teams Use The Dark Web To Track Threats?
The term “onion routing” reflects how layers of encryption are applied—similar to peeling layers from an onion. With each hop through the network, a layer of encryption is removed, concealing the user’s original location and identity. The dark web is just misinterpreted; it is not intrinsically dangerous. Used ethically, such as for privacy or study, one can search this area lawfully and safely. Combined with smart surfing behaviour and technologies like Tor and a VPN, even the darkest reaches of the internet may be securely traversed. Stay informed about the latest darknet marketplaces, secure browsing practices, and privacy tools.
It collects data from the public Tor network and archives historical data of the Tor ecosystem. The website is available on the surface web and has a .onion site. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime.

In addition, even if the Tor node fails, your data won’t be exposed because the VPN’s encryption still holds up. As mentioned, we recommend using a safe provider like NordVPN, which also offers Onion Over VPN servers perfect for accessing the dark web safely. One of the challenges of exploring the dark web is that you can’t just use a search engine and type in what you’re after like you would on the surface web. Instead, you often have to consult directories to find lists of legitimate sites and visit and access them that way or use special dark web-friendly search engines. Given the many cyber threats present on the dark web, it’s recommended to be extra careful when you access it. While we discourage engaging in illegal activities, there are legitimate websites and forums on the Dark Web that promote privacy, cybersecurity, and digital rights.
The dark web is home to plenty of unlawful activity, so you must ensure you never get involved in something illegal. ExpressVPN protects your internet traffic using 256-bit AES channel strong encryption together with 4096-bit DHE-RSA keys and a SHA512 hash authentication. The company has an independently audited no-logs policy and its comprehensive server network is RAM-only. It comes with DNS leak protection and works well if you’re aiming to improve online privacy. The history of the Dark Web is intricately tied to the development of internet technology and the ongoing pursuit of online anonymity. The concept of an encrypted, hidden layer of the internet began taking shape in the 1990s.
- You can eliminate these privacy concerns by connecting to a VPN before launching the Tor Browser in a setup called Tor over VPN.
- ExpressVPN’s intuitive apps work on up to 8 devices at a time, ensuring protection for the entire family.
- Think of it as an iceberg, with only a tiny part visible above the surface.
- The dark web is a part of the internet that you only step into with a specific tool (Tor, more on this later in the article).
Step 7: Use Additional Security Tools
Using a virtual private network (VPN) masks your real IP by routing your internet traffic through a secure server, making it appear as though you’re browsing from a different location. A VPN also encrypts your connection, keeping your data safe from surveillance and unauthorized access. The dark web is a mysterious and hidden part of the internet that cannot be accessed through traditional search engines. While it is known for its association with illegal activities, it is important to note that not everything on the dark web is illegal, and there are legitimate uses for it as well. This article aims to provide key points about the dark web and offer tips on navigating it safely to protect your online security. While the Dark Web is infamous for its association with illegal activities, it is important to acknowledge that there are legal uses as well.
Links and downloads can be disguised as something innocuous but contain malware, viruses, or other malicious software. Only click on trusted links and download files from reputable sources. Minimize the use of your real name, address, phone number, or any other personally identifiable information. Adopt a pseudonym or anonymous username to help protect your identity. Stay informed about the latest security practices and developments related to the Dark Web.



